key cybersecurity tips for your organization to implement in 2024
Cybersecurity attacks are increasingly common. During this digital age, most people’s whole lives happen online. Many rely on the internet to shop, communicate with their loved ones, or just learn.
Also, many organization owners connect multiple devices and network them to run their operations.
However, it can allow attackers to use some entry points to access key information. Therefore, knowing and understanding the best practices in cyber security is essential to protect your data.
While they won’t prevent all attacks, these cyber tips can help lessen the risks and protect your devices from cyberattacks. Find them below!
Main Cybersecurity Tips for Organization
Tips for your organization are shown below –
Update Your Devices and Apps
If you get a notification about an update for your apps or devices, install it! Many think they only offer more features.
However, these updates also bring security patches to fix certain vulnerabilities that attackers could use to access your system and, consequently, your data.
When your device doesn’t receive updates, upgrading it or buying a newer model is the best option.
Overall, these are the Internet-security best practices to consider:
- Keep your devices up-to-date
- Update their apps and software or set them to update automatically
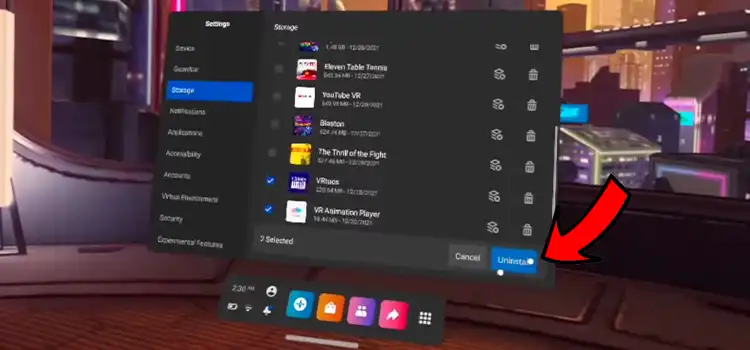
- Delete apps you don’t use
Keep your Antivirus Software Updated
An antivirus software solution is indispensable for most devices. Therefore, keeping it up to date is one of the best practices in cyber security.
These antivirus solutions usually scan devices to detect ransomware, spyware, and any other malicious threats that could put your privacy, security, and Organization at risk.
Here are the best computer security and safety tips to consider:
- Choose antivirus software with firewall options to protect your devices and networks from cyber threats
- Update your antivirus software and scan for malicious threats several times during the year
- Keep up to date with the latest IT security best practices and fixes to protect your devices from data breaches and ransomware attacks
Back-Up Your Key Data
When it comes to Internet security best practices, one of the other most important things you can do is back up your devices’ data. You only have to copy that information to a separate location.
Backing up your data can help you avoid losing key details if you are targeted by a cyber attack and cannot access your computers or phones.
These are the best data backup and recovery tips you can leverage for your Organization:
- Back up your data weekly
- Do a cold or offline backup using an external hard drive
- Sign up for cloud-based services, such as Dropbox, for a cloud backup
- Backup all your devices
How Spin.ai Can Support Your Cybersecurity Efforts
Spin.ai is an all-in-one platform offering SaaS security and ransomware protection to all organizations.
In addition, Spin technology has different features that can support your company’s cybersecurity best practices, such as backup and recovery, data leak prevention, and risk assessment options.
Ensure Password Hygiene
Password hygiene is another cybersecurity best practice for organization owners. However, it’s often forgotten.
Ideally, you shouldn’t use the same password for all your online accounts. Instead, you must ensure each has a unique password with different characters.
Here’s what you should do to ensure password hygiene at your company:
- Use different passwords for all your online accounts
- Create passwords with multiple numbers, symbols, and letters
- Use passwords with 12-16 characters
- Avoid repeating characters
- Don’t include personal information
- Store your passwords in a reliable password manager
- Use passphrases if possible
Turn on Two-factor Authentication
During the past few years, two-factor authentication (2FA) has been a game changer for cybersecurity. It’s one of the best tools to prevent hackers from accessing your online accounts.
If you turn on two-factor authentication, you must enter a code you get through a device, such as your phone, to access your online accounts.
Therefore, even if an attacker manages to crack your password, they won’t be able to get into your account if they don’t have your phone.
Here’s how you can use two-factor authentication:
- Always turn on two-factor authentication for your email or social media accounts (Some payment platforms also allow you to turn this option on)
- Choose other authentication options instead of SMS
Don’t Click on Unfamiliar or Suspicious Emails or Links
Phishing scams are common to hack another person’s device and get their credentials. Some even used it to steal identities.
Although most antivirus programs contain protection against phishing, you should be careful and avoid clicking on messages or links that may take you to fraudulent websites where hackers can obtain your login credentials.
What can you do to avoid phishing scams?
- Hackers use phishing scams to lead users to fraudulent sites and obtain their credentials directly from them. Therefore, the only way to combat these threats is by avoiding clicking on unfamiliar or suspicious emails, attachments, texts, messages, and links.
Write Creative Answers to Your Recovery Questions
Creativity can also be part of your organization’s computer security best practices. What answers did you set for your accounts’ recovery questions?
These questions are often used to confirm your identity and help you recover your password if you forget it. However, even though they’re often based on basic things you can remember about yourself, it doesn’t mean you can’t get creative.
If you set easy answers, like your mom’s middle name or the country you were born in, attackers can gain access to your account in less time than you think.
Therefore, you should always do the following:
- Set original answers and be creative instead of honest
- Always set answers you can remember, even if they aren’t easy or common
Don’t Make Sensitive Transactions on Free-WiFi
The best cyber security guidelines also include recommendations on what not to do if you want to protect your online accounts and data. Avoiding sensitive transactions if you’re using free-wifi is one of them.
When using free wifi or a hotspot, be careful what you do online, as these networks are often insecure.
Also, if you’re using free wifi, you may be at risk of suffering “shoulder surfing.” It means that someone else can see over your shoulders to try to catch your account’s login credentials.
Cyber tips to avoid attacks if you use free wifi:
- Turn on your two-factor authentication before checking your email
- Don’t do online shopping or internet banking
- Always try to use your own devices
Other Internet Security Tips You Should Consider
Besides the recommendations mentioned above, you can also do the following:
- Educate your employees on cybersecurity best practices
- Define a clear online behavior policy
- Do a password review to know if yours are secure enough
- Use social media carefully
- Don’t share personal information on the internet
- Use a reliable data-protection platform, such as Spin.ai
Final Thoughts
While they can’t prevent all possible attacks, these cybersecurity tips can reduce risks and help combat threats. Leverage them to protect your organization’s online accounts today!
Subscribe to our newsletter
& plug into
the world of technology